| |
|
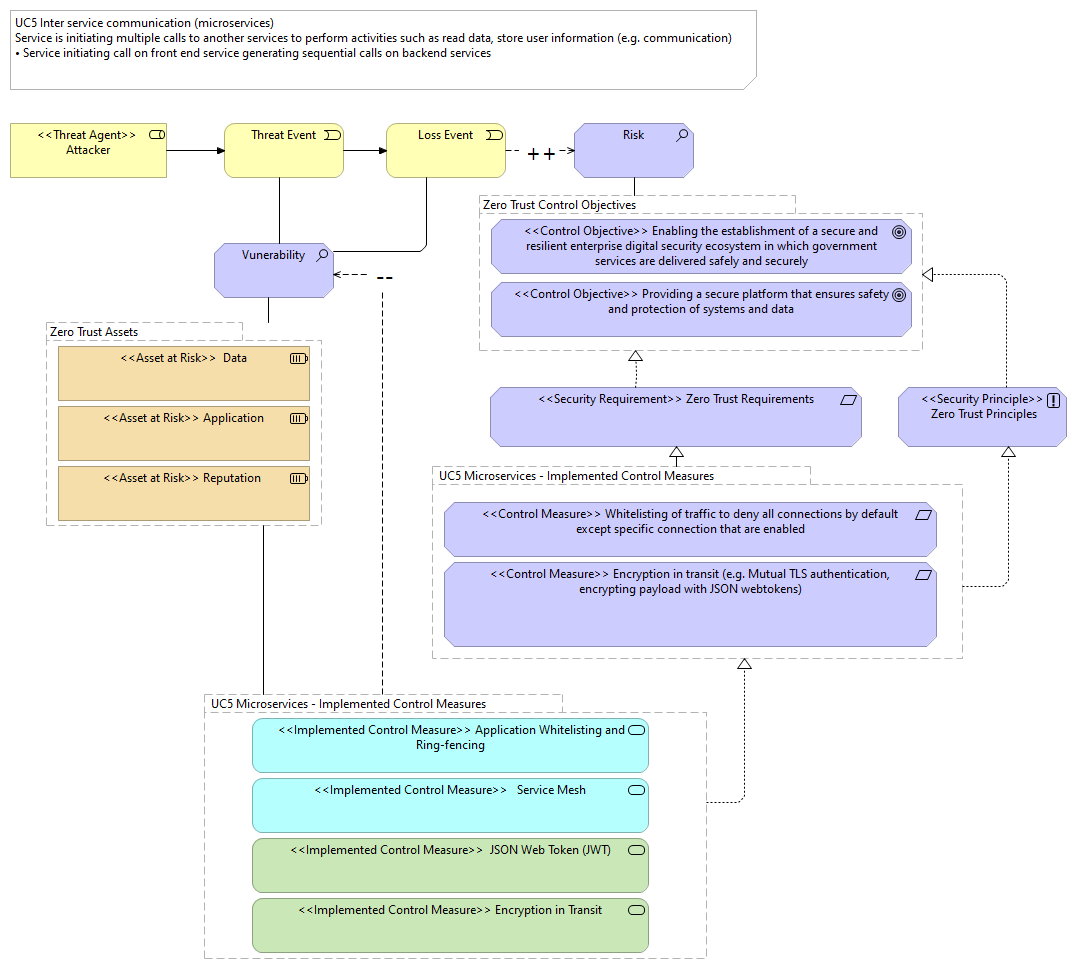
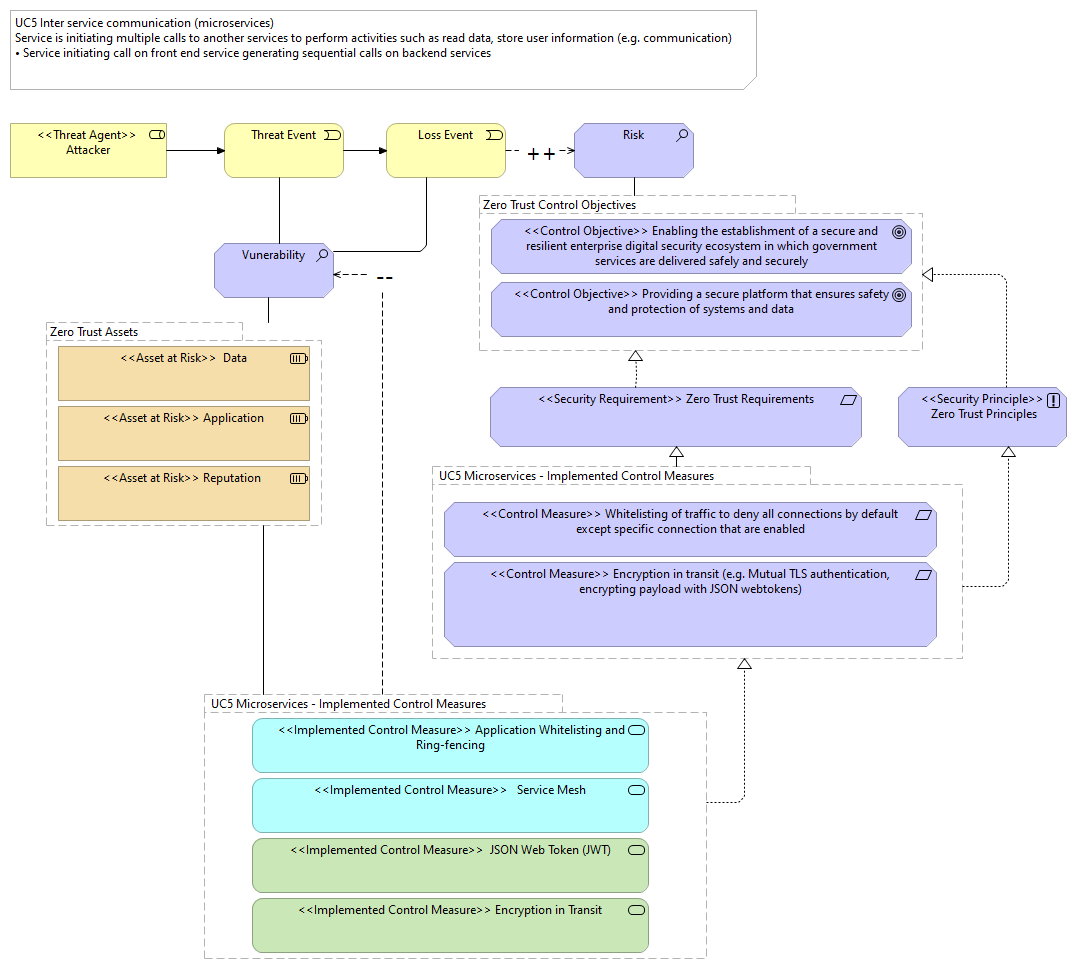
UC5 Microservices - Implemented Control Measures |
<<Control Measure>> Whitelisting of traffic to deny all connections by default except specific connection that are enabled |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Control Measure>> Encryption in transit (e.g. Mutual TLS authentication, encrypting payload with JSON webtokens) |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Security Requirement>> Zero Trust Requirements |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Security Principle>> Zero Trust Principles |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Implemented Control Measure>> Encryption in Transit |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Implemented Control Measure>> Application Whitelisting and Ring-fencing |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Implemented Control Measure>> Service Mesh |
| |
|
UC5 Microservices - Implemented Control Measures |
<<Implemented Control Measure>> JSON Web Token (JWT) |
| |
|
UC5 Microservices - Implemented Control Measures |
UC5 Microservices - Implemented Control Measures |
| |
|
UC5 Microservices - Implemented Control Measures |
Vunerability |
| |
|
Zero Trust Assets |
<<Asset at Risk>> Application |
| |
|
Zero Trust Assets |
<<Asset at Risk>> Reputation |
| |
|
Zero Trust Assets |
<<Asset at Risk>> Data |
| |
|
Zero Trust Assets |
UC5 Microservices - Implemented Control Measures |
| |
|
Zero Trust Control Objectives |
Risk |
| |
|
Zero Trust Control Objectives |
<<Control Objective>> Enabling the establishment of a secure and resilient enterprise digital security ecosystem in which government services are delivered safely and securely |
| |
|
Zero Trust Control Objectives |
<<Control Objective>> Providing a secure platform that ensures safety and protection of systems and data |
| |
|
<<Threat Agent>> Attacker |
Threat Event |
| |
|
Threat Event |
Loss Event |
| |
|
Threat Event |
Vunerability |
| |
|
Loss Event |
Vunerability |
| |
|
Loss Event |
Risk |
| |
|
Vunerability |
Zero Trust Assets |
| |
|
<<Security Principle>> Zero Trust Principles |
Zero Trust Control Objectives |
| |
|
<<Security Requirement>> Zero Trust Requirements |
Zero Trust Control Objectives |